Extended detection & response
ESET Inspect
Provides risk managers and incident responders with outstanding threat and system visibility, allowing them to perform fast and in-depth root cause analysis and immediately respond to incidents.
Paired with the time-tested prevention power of ESET Endpoint Protection products, ESET Inspect is a cloud-delivered, XDR-enabling solution to:
- Detect advanced persistent threats
- Stop fileless attacks
- Block zero-day threats
- Protect against ransomware
- Prevent company policy violations
Explore features
Public API
ESET Enterprise Inspector features an API that enables accessing and exporting of detections and their remediation to allow effective integration with tools such as SIEM, SOAR, ticketing tools and many others.
Multiplatform coverage
ESET Enterprise Inspector supports Windows and macOS, which makes it a perfect choice for multiplatform environments
Remote access
ESET Enterprise Inspector features remote PowerShell capabilities that allow Security Engineers to remotely inspect and configure their organization’s computers, so a sophisticated response can be achieved without breaking the user’s workflow.
Threat Hunting
Apply data filters to sort it based on file popularity, reputation, digital signature, behavior or contextual information. Setting up multiple filters allows automated, easy threat hunting, including APTs and targeted attacks, which is customizable to each company’s environment. By adjusting behavior rules, ESET Enterprise Inspector can also be customized for Historic Threat Hunting and “rescan” the entire events database.
One-click isolation
Define network access policies to quickly stop malware’s lateral movements. Isolate a compromised device from the network by just one click in the ESET Enterprise Inspector interface. Also, easily remove the devices from the containment state.
Open architecture & integrations
ESET Enterprise Inspector provides a unique behavior and reputation-based detection that is fully transparent to security teams. All rules are easily editable via XML to allow fine-tuning or easily created to match the needs of specific enterprise environments, including SIEM integrations.
MITRE ATT&CK™
ESET Enterprise Inspector references its detections to the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK™) framework, which in one click provides you with comprehensive information even about the most complex threats.
Live response options
Our XDR comes packed with easily accessible oneclick response actions such as rebooting and shutting down an endpoint, isolating endpoints from the rest of the network, running an on-demand scan, killing any running process, and blocking any application based on its hash value. Additionally, thanks to ESET Inspect’s live response option, called Terminal, security professionals can benefit from the full suite of investigation and remediation options in PowerShell.
Root Cause Analysis
Easily view the root cause analysis, and full process tree, of any potentially malicious chain of events, drill down to the desired level of detail and make informed decisions based on the rich provided context and explanations for both benign and malicious causes, written by our malware experts.
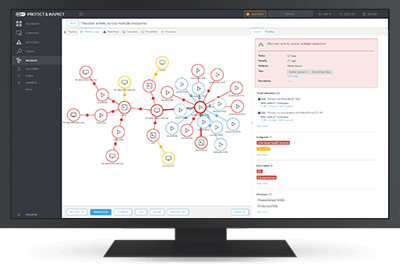
Automated incident visualization
Get perfect visibility with automatically created and clearly visualized incidents. ESET Inspect correlates vast amounts of data to find root cause events and compile them into comprehensive incidents so that you can resolve them immediately.
Automation and customization
Easily tune ESET Inspect to the level of detail and automation you need. At setup, choose how much interaction and data storage you want, then let Learning Mode map your environment and suggest settings.
Reputation system
Extensive filtering enables security engineers to identify every known good application, using ESET’s robust reputation system, so your security teams can focus on threats, not false positives.
Flexibility of deployment
We let you decide how to deploy your security solution: It can run via your own servers on-prem, or via a cloudbased installation, allowing you to tune your setup according to your TCO targets and hardware capacity.