- A Russian-aligned aligned threat actor spread war-related disinformation to Ukrainian readers via spam emails.
- The spearphishing campaign targeted a Ukrainian defense company and an EU agency.
- Due to the similarities in the network infrastructure used in these PSYOPs and phishing operations, ESET research can say with high confidence that they are linked.
- Operation Texonto loosely resembles Russia-aligned Callisto APT group activities; however, ESET Research does not have enough evidence to attribute the operations to any specific group.
- In the first wave of disinformation emails in November 2023, the Russia-aligned threat actors tried to influence and demoralize Ukrainian citizens with disinformation messages about war-related topics. The second wave in December 2023 was even darker in tone.
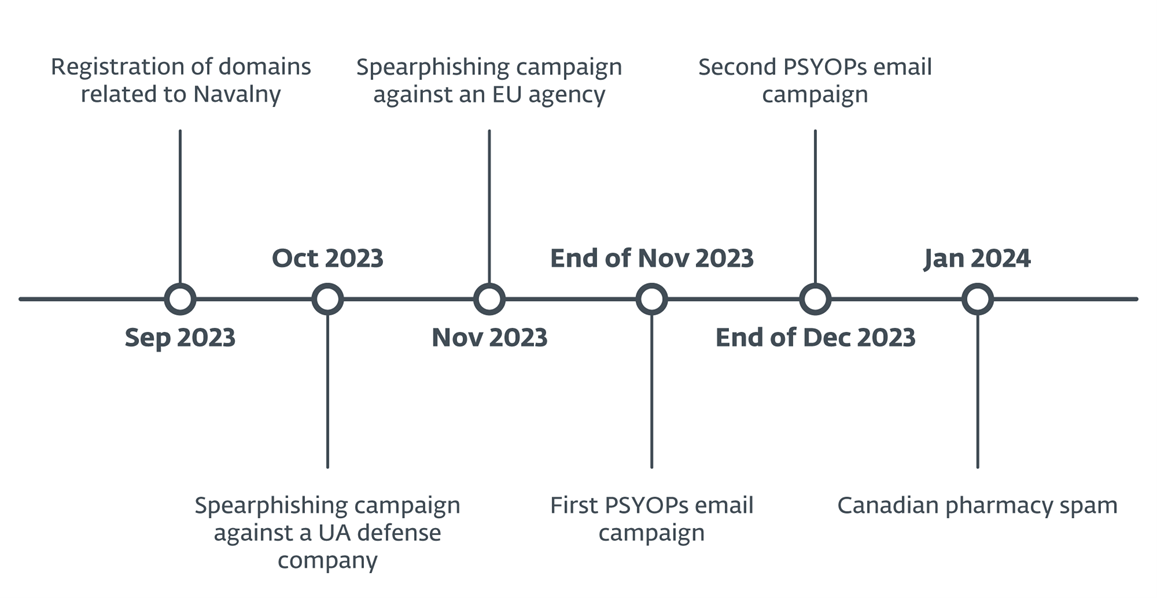
BRATISLAVA, MONTREAL — February 21, 2024 — ESET Research recently discovered Operation Texonto, a disinformation/psychological operations (PSYOPs) campaign using spam emails as the main distribution method. Via messages sent in two waves of PSYOPs, the Russia-aligned threat actors tried to influence and demoralize Ukrainian citizens with disinformation messages about war-related topics. The first wave took place in November 2023 and the second one at the end of December 2023. The contents of the emails were about heating interruptions, drug shortages, and food shortages, which are typical themes of Russian propaganda. Additionally, in October 2023, ESET detected a spearphishing campaign that targeted a Ukrainian defense company, and one targeting an EU agency in November 2023 utilizing standard-looking fake Microsoft login pages. The goal of both was to steal credentials for Microsoft Office 365 accounts. Due to the similarities in the network infrastructure used in these PSYOPs and phishing operations, ESET research can say with high confidence that they are linked.
“Since the start of the war in Ukraine, Russia-aligned groups such as Sandworm have been busy disrupting Ukrainian IT infrastructure using wipers. In recent months, we have observed an uptick in cyberespionage operations, especially by the infamous Gamaredon group. Operation Texonto shows yet another use of technologies to try to influence the war,” says ESET researcher Matthieu Faou, who discovered Operation Texonto.
“The strange brew of espionage, information operations, and fake pharma messages can only remind us of Callisto, a well-known Russia-aligned cyberespionage group, some members of which were the subject of an indictment by the U.S. Department of Justice in December 2023. Callisto targets government officials, staff in think tanks, and military-related organizations via spearphishing websites designed to mimic common cloud providers. The group has also run disinformation operations such as a document leak just ahead of the 2019 UK general election. Finally, pivoting on its old network infrastructure leads to fake pharma domains,” continues Faou. However, he concludes: “While there are several high-level points of similarity between Operation Texonto and Callisto operations, we haven’t found any technical overlap, and we currently do not attribute Operation Texonto to a specific threat actor. However, given the TTPs, targeting, and the spread of messages, we attribute the operation with high confidence to a group that is Russia aligned.”
An email server, operated by the attackers and used to send the PSYOPs emails, was reused two weeks later to send typical Canadian pharmacy spam. This category of illegal business has been very popular within the Russian cybercrime community for a long time. A few more pivots also revealed domain names that are part of Operation Texonto and related to internal Russian topics, such as Alexei Navalny, the well-known Russian opposition leader who was in jail and died on 2024-02-16. This means that Operation Texonto probably includes spearphishing or information operations targeting Russian dissidents and supporters of the late opposition leader.
The goal of the first wave of disinformation emails was to sow doubt in the minds of Ukrainians; for instance, one email says “There may be heating interruptions this winter.” Others purportedly from the Ministry of Health talk about medicine shortages. It doesn’t seem that there were any malicious links or malware in this specific wave, only disinformation. One domain masquerading as the Ministry of Agrarian Policy and Food of Ukraine recommended replacing unavailable medicine with herbs. In yet another email “from” the Ministry, they suggest eating “pigeon risotto” a photo of a live pigeon and a cooked pigeon. Those documents were purposely created in order to rile up and demoralize the readers. Overall, these fake messages align with common Russian propaganda themes. They are trying to make Ukrainian people believe they won’t have drugs, food, and heating because of the Russia-Ukraine war.
About a month after the first wave, ESET detected a second PSYOPs email campaign targeting not only Ukrainians, but also people in other European countries. The targets are somewhat random, ranging from the Ukrainian government to an Italian shoe manufacturer. According to ESET telemetry, a few hundred people received emails in this wave. The second wave was darker in its messaging, with the attackers suggesting people amputate a leg or an arm to avoid military deployment. Overall, it has all the characteristics of PSYOPs during wartime.
ESET products and research have been protecting Ukrainian IT infrastructure for many years. And since the start of the Russian invasion in February 2022, ESET Research has prevented and investigated a significant number of attacks launched by Russia-aligned groups.
For more technical information about Operation Texonto, check out the blogpost “Operation Texonto: Information operation targeting Ukrainian speakers in the context of the war” on WeLiveSecurity.com. Make sure to follow ESET Research on Twitter (today known as X) for the latest news from ESET Research.
Timeline of Operation Texonto
About ESET
For more than 30 years, ESET® has been developing industry-leading IT security software and services to protect businesses, critical infrastructure and consumers worldwide from increasingly sophisticated digital threats. From endpoint and mobile security to endpoint detection and response, as well as encryption and multifactor authentication, ESET’s high-performing, easy-to-use solutions unobtrusively protect and monitor 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company that enables the safe use of technology. This is backed by ESET’s R&D centers worldwide, working in support of our shared future. For more information, visit www.eset.com or follow us on LinkedIn, Facebook, and X (Twitter).