Extended detection & response
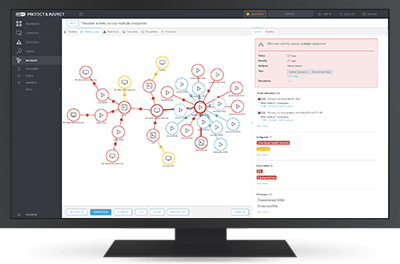
ESET Inspect
Provides risk managers and incident responders with outstanding threat and system visibility, allowing them to perform fast and in-depth root cause analysis and immediately respond to incidents.
Paired with the time-tested prevention power of ESET Endpoint Protection products, ESET Inspect is a cloud-delivered, XDR-enabling solution to:
- Detect advanced persistent threats
- Stop fileless attacks
- Block zero-day threats
- Protect against ransomware
- Prevent company policy violations
Explore features
Public API
ESET Inspect features a Public REST API that enables the accessing and exporting of detections and their remediation to allow effective integration with tools such as SIEM, SOAR, ticketing tools and many others.
Multiplatform coverage
ESET Inspect supports Windows, macOS, and Linux, which makes it a perfect choice for multiplatform environments.
Save and smooth remote access
Incident response and security services are only as smooth as the ease with which they are accessed – both in terms of the incident responder’s connection to the XDR console, and the connection with the endpoints. The connection works at close to real-time speed with maximum security measures applied, all without the need for third-party tools.
Threat Hunting
Use the powerful query-based IOC search and apply filters to raw data for sorting based on file popularity, reputation, digital signature, behavior, or other contextual information. Setting up multiple filters allows automated, easy threat hunting and incident response, including the ability to detect and stop APTs and targeted attacks.
One-click isolation
Define network access policies to quickly stop lateral movement by malware. Isolate a compromised device from the network with just one click in the ESET Inspect interface. Also, easily remove devices from the containment state.
Open architecture & integrations
ESET Inspect provides unique behavior- and reputationbased detection that is fully transparent to security teams. All rules are easily editable via XML to allow finetuning or easily created to match the needs of specific enterprise environments, including SIEM integrations.
MITRE ATT&CK™
ESET Inspect references its detections to the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK™) framework, which in one click provides you with comprehensive information even about the most complex threats.
Investigation and Remediation
Use a built-in set of rules or create your own rules to respond to detected incidents. Each triggered alarm features a proposed next step to be performed for remediation. This quick response functionality helps to ensure that any single incident will not fall through the cracks.
Anomaly and behavior detection
Check actions carried out by an executable and utilize ESET’s LiveGrid® Reputation system to quickly assess if executed processes are safe or suspicious. Monitoring anomalous user-related incidents are possible due to specific rules written to be triggered by behavior, not simple malware or signature detections. Grouping of computers by user or department allows security teams to identify if the user is entitled to perform a specific action or not.
Company Policy Violation Detection
Block malicious modules from being executed on any computer in your organization’s network. ESET Enterprise Inspector’s open architecture offers the flexibility to detect violations of policies about using specific software like torrent applications, cloud storage, tor browsing or other unwanted software.
Tagging
Assign and unassign tags for fast filtering to EEI objects such as computers, alarms, exclusions, tasks, executables, processes and scripts. Tags are shared among users, and once created, they can be assigned within seconds.
Scoring
Prioritize the severity of alarms with scoring functionality that attributes a severity value to incidents and allows the admin to quickly identify computers with a higher probability of a potential incident.
Multiple Indicators of compromise
View and block modules based on over 30 different indicators, including hash, registry modifications, file modifications and network connections.
Data collection
View comprehensive data about a newly executed module, including time of execution, user who executed, dwell time and attacked devices. All data is locally stored to prevent sensitive data leakage.